|
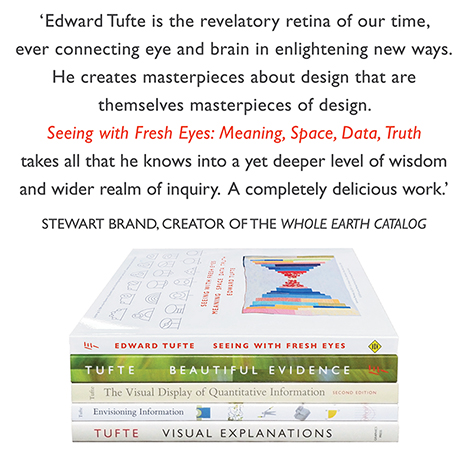
All 5 books, Edward Tufte paperback $180
All 5 clothbound books, autographed by ET $280
Visual Display of Quantitative Information
Envisioning Information
Visual Explanations
Beautiful Evidence
Seeing With Fresh Eyes
catalog + shopping cart
|
Edward Tufte e-books Immediate download to any computer: Visual and Statistical Thinking $5
The Cognitive Style of Powerpoint $5
Seeing Around + Feynman Diagrams $5
Data Analysis for Politics and Policy $9
catalog + shopping cart
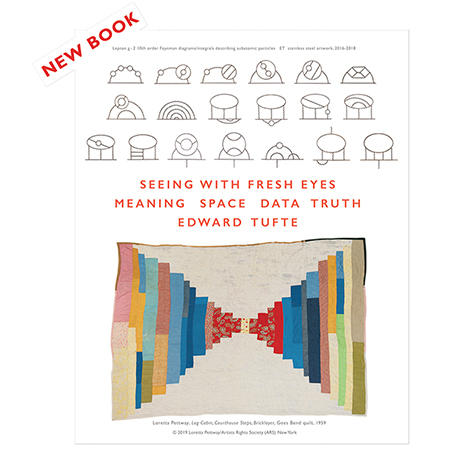
New ET Book
Seeing with Fresh Eyes:
catalog + shopping cart
Meaning, Space, Data, Truth |
Analyzing/Presenting Data/Information All 5 books + 4-hour ET online video course, keyed to the 5 books. |
A useful way to monitor access attempts to your computer is Little Snitch 2. LS2 is described by its developer as follows:
"As soon as you're connected to the Internet, applications can potentially send whatever information they want to wherever they want.Sometimes they do this for good reason, on your explicit request. But often they don't. Little Snitch allows you to intercept these unwanted connection attempts, and lets you decide how to proceed.
Little Snitch informs you whenever a program attempts to establish an outgoing Internet connection. You can then choose to allow or deny this connection, or define a rule how to handle similar, future connection attempts. This reliably prevents private data from being sent out without your knowledge. Little Snitch runs inconspicuously in the background and it can also detect network related activity of viruses, trojans and other malware."
Here's a recent report that indicates Adobe CS3 InDesign calls home to a web monitoring/marketing agency when the user opens InDesign. The IP number given by Little Snitch, upon an IP search, identified the agency as Omniture. Is Adobe a client of Omniture or Ominture a client of Adobe?
-- Edward Tufte
Wireshark is the sort of packet sniffing software the article above mentions, which can be used to find out what InDesign or other programs might be trying to tell the Big Brother Inc. once Little Snitch alerts you to their transgressions.
-- Niels Olson (email)
Little Snitch is for Apple OSX only. For Windows users I'd recommend Zone Alarm, which comes in various versions, though I've found the basic, free version to be sufficient for my own needs.
Zone Alarm version comparison
-- Dan Roberts (email)
I think most commercial firewalls also include this capability, though it's often turned off by default. If you already have a commercial firewall, check your manual.
-- Tom (email)
A screenshot from Apple's browser of the "Reset Safari" dialogue box that allows users to clear out browser debris:
 |
Today, 10 minutes of surfing through various news sites (NYTimes, Valleywag, Silicon Alley Insider, Arts & Letters Daily, and several others) generated about 100 cookies in my browser cookie file, which all promptly vanished with the Reset.
Several years ago there was a claim that the flaw in Internet Explorer allowed malicious external access to a user's browser history file and cookie file. An entertaining use of cookies to set a cookie in the browser of a malicious contributor to a board, a cookie that blocks access to the board. Cookies mainly serve marketing purposes by tracking user browsing habits. Delete them regularly. Also allow only the site visited to set a cookie by means of your browser preferences.
To see the live setting of cookies on your computer, open up the browser cookie file (usually in security preferences) in a separate window as you are visiting websites.
-- Edward Tufte
I am a big fan of Safari, but cookie handling is one area where I've found that Firefox outshines it. It is fairly easy to set Firefox to accept cookies only for the current session (deleting cookies when the browser is closed), while allowing cookies from specific sites to survive across sessions. This allows the user to stay logged in to selected sites, like Gmail or Yahoo, while ensuring that the marketing-related cookies are deleted whenever she closes the browser. Mungo Says Bah has a nice instruction for setting this up.
Not mentioned in that instruction is that you can have both the "exceptions" and the "show cookies" (or "view cookies") dialogs open at the same time, making it easier to see which domains have set cookies and properly set up the exceptions list.
-- Tom (email)
Sears spyware
Sears seems to have installed spyware on the personal computers of customers in the Sears "Community" link. The CA Security Advisor Research Blog reports that the Sears spyware reports the following user data to a market research company:
"Here is a summary of what the software does and how it is used. The proxy: 1. Monitors and transmits a copy of all Internet traffic going from and coming to the compromised system. 2. Monitors secure sessions (websites beginning with `https'), which may include shopping or banking sites. 3. Records and transmits "the pace and style with which you enter information online..." 4. Parses the header section of personal emails. 5. May combine any data intercepted with additional information like "select credit bureau information" and other sources like "consumer preference reporting companies or credit reporting agencies". In addition, My SHC Community requires a variety of personal information during registration - like name, email, address, city, state, and age. All of this information can be correlated with intercepted data to create a comprehensive profile."Now Brian Krebs of The Washington Post (in his superb column Security Fix) reports that these Sears "community" shopping habits have been made publicy searachable link.
Marketeers who track customers and websites (such as Google) that track their users are a major threat to privacy, probably much more so than the government.
Some of the activities detected above were revealed by Wireshark (described in a contribution above).
-- Edward Tufte
Helpful advice from Paul Boutin, Slate, December 27, 2007: http://www.slate.com/id/2180881
-- Edward Tufte
I installed Little Snitch when the suggestion first appeared in this thread, and I've found it interesting to see which programs try to connect and how often they do it, but less worrying than I expected: virtually all the attempted connections from my computer seem to be legitimate. In addition, I expected Word to be a major offender, but it hasn't attempted to make a connection even once. Unlike most people I very rarely run Word, so it's not normally running (if I really must produce a .doc file I use Pages), but recently I've had it on just to see what it does, and the answer is mostly nothing. I had a similar experience with PowerPoint, which, again, I just fired up for a short time to see if it would try to do anything I didn't want, but like Word it just sat there doing nothing.
-- Athel Cornish-Bowden (email)
AT&T, NBC, and others want network-level packet-sniffing
AT&T and Other ISPs May Be Getting Ready to Filter. If the internet was wholly and solely privately financed, the case would be hard to make against this. However, there is vast public investment in the networks. Enormous amounts of technology is developed by tax-funded universities and other government agencies (NIST and NSA, for example, drive a fair amount of cryptography development through competitions) and taxpayer dollars have directly paid for the network (like the $3 billion for fibre optic networking that the ISPs never built, and the root servers of the internet).
Instead, the ISPs would like to use Wireshark-like technology on an industrial level to sniff your packets and only allow those to pass that they deem appropriate. And appropriateness will apparently be defined by NBC and other media companies, who have so miserably failed the public interest since the radio spectrum was first regulated as a public resource almost 100 years ago. It may not be long before every site has to use SSL certificates ("https") and tunnel all services through ports 80 and 443 just to provide their services to people. This would be both technically annoying (perhaps even difficult) and less secure than protocol-port-daemon dogma that has worked well for decades.
At least the ISPs intend to be "friendly" when they censor.
-- Niels Olson (email)
Ryan Singel at Wired has a great column, Threat Level, including this short analysis piece on the Protect America Act, which allows intelligence agencies to compel ISPs, cell phone companies, and others (like search engines) to supply information, and even if that information turns out to be domestic, they have up to six months before they have to tell the service provider. No mention of informing the potential victim. And the oversight committees are only informed of instances where the act's procedures are violated. How could the oversight committees even test their effectiveness?
The act itself seems almost privacy-protective when read out of context. Singel does a pretty good job of itemizing some of the actual implications that come with context. Singel links to the text of the Protect America Act but to put it in context yourself, here's the text of FISA. In theory, any internet site with a database of comments and with operations in the US could be compelled to release information.
A couple of other things to keep in mind: (1) the weakest link in intel is and will probably always be human intelligence assets, and that includes linguists. A few comp sci, math and physics nerds with computers can develop pretty sophisticated analysis techniques, even for huge amounts of raw data. Translating unique conversations, however, takes grey matter, 3 pounds at a time. (2) Even if you have the linguists, people developing attack plans inside their target country, with plans nearing an actionable stage, are almost certain to be using freely available PGP encryption, like GNU Privacy Guard, and anonymizing proxies, like Tor. Finally, once a plan has gone live the timeline moves so fast that neither encryption nor intercepts matter. So who will get caught in this net?
-- Niels Olson (email)
To Tom and other Safari fans, it is possible to get Safari to store cookies only until you quit Safari by "locking" the Cookies.plist file; that is, marking it read-only:
http://www.macosxhints.com/article.php?story=20031026012426123
I've found that after clearing cookies as depicted in ET's 12/31 post, it's useful to visit a small number of trusted sites before locking Cookies.plist down—there are three or four systems at work that store login credentials in a cookie, and I read the New York Times often enough that logging in repeatedly is annoying. This is essentially a poor man's exception management system for Safari users.
-- Josh Daghlian (email)